BlueTeamSec
- Following NoName057(16) DDoSia Project’s Targetsblog.sekoia.io Following NoName057(16) DDoSia Project’s Targets
DDoSia is a DDoS attack toolkit used by the pro-Russia hacktivist group NoName057(16) against countries critical the invasion of Ukraine.

- Process Mockingjay: Echoing RWX In Userland To Achieve Code Executionwww.securityjoes.com Process Mockingjay: Echoing RWX In Userland To Achieve Code Execution
Our research team is committed to continuously identifying potential security vulnerabilities and techniques that threat actors may exploit to bypass existing security controls. In this blog post, our team is detailing on a comprehensive research specifically focused on process injection techniques ...

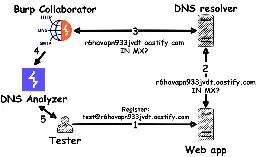
- DNS Analyzer - Finding DNS vulnerabilities with Burp Suitesec-consult.com DNS Analyzer - Finding DNS vulnerabilities with Burp Suite
A brand-new Burp Suite extension for discovering DNS vulnerabilities in web applications.
- Research: Zero-Day Shopwww.cyfirma.com Research Report : Zero Day Shop - CYFIRMA
EXECUTIVE SUMMARY The CYFIRMA research team has identified a new marketplace run by unknown threat actors, known as the Zero-Day...

- Bluepurple Pulse: week ending June 25thbluepurple.binaryfirefly.com Bluepurple Pulse: week ending June 25th
DDoS can have global cloud scale impact in 2023..
- Beyond the Horizon: Traveling the World on Camaro Dragon’s USB Flash Drivesresearch.checkpoint.com Beyond the Horizon: Traveling the World on Camaro Dragon’s USB Flash Drives - Check Point Research
Executive summary Introduction In early 2023, CPIRT investigated an incident at a European hospital. The investigation showed that the malicious activity observed was likely not targeted but was simply collateral damage from Camaro Dragon’s self-propagating malware infections spreading via USB drive...

- Graphican: Flea Uses New Backdoor in Attacks Targeting Foreign Ministriessymantec-enterprise-blogs.security.com Graphican: Flea Uses New Backdoor in Attacks Targeting Foreign Ministries
Backdoor leverages Microsoft Graph API for C&C communication.

- Dissecting TriangleDB, a Triangulation spyware implantsecurelist.com Dissecting TriangleDB, a Triangulation spyware implant
In researching Operation Triangulation, we set ourselves the goal to retrieve as many parts of the exploitation chain as possible. As of now, we have finished analyzing the spyware implant and are ready to share the details.

- Unpacking RDStealer: An Exfiltration Malware Targeting RDP Workloadswww.bitdefender.com Unpacking RDStealer: An Exfiltration Malware Targeting RDP Workloads
In June 2023, Bitdefender Labs published a research paper about espionage operation in East Asia.
- BlueDelta Exploits Ukrainian Government Roundcube Mail Servers to Support Espionage Activitieswww.recordedfuture.com BlueDelta Exploits Ukrainian Government Roundcube Mail Servers to Support Espionage Activities | Recorded Future
A new report details a campaign by the threat actor, BlueDelta, likely intended to enable intelligence-gathering to support Russia’s invasion of Ukraine.
- CID Lookout: Unsolicited Smartwatches Received by Mailwww.cid.army.mil CID Lookout: Unsolicited Smartwatches Received by Mail
Service members across the military have reported receiving smartwatches unsolicited in the mail. These smartwatches, when used, have auto-connected to Wi-Fi and began connecting to cell phones
- win32-app-isolation: Tools and documentation for Win32 app isolationgithub.com GitHub - microsoft/win32-app-isolation: Tools and documentation for Win32 app isolation
Tools and documentation for Win32 app isolation. Contribute to microsoft/win32-app-isolation development by creating an account on GitHub.
- openfire鉴权绕过漏洞原理解析 - Openfire Authentication Bypass Vulnerability Principle Analysismp-weixin-qq-com.translate.goog openfire鉴权绕过漏洞原理解析
Openfire是根据开放源 Apache 许可获得许可的实时协作(RTC)服务器。它使用唯一被广泛采用的用于即时消息的开放协议 XMPP(也称为 Jabber)。Openfire 的设置和管理非常简单,但是却提供了坚实的安全性和性能。
- Inside of the WASP's nest: deep dive into PyPI-hosted malwareblog.virustotal.com Inside of the WASP's nest: deep dive into PyPI-hosted malware
Photo by Matheus Queiroz on Unsplash In late 2022 we decided to start monitoring PyPI , arguably the most important Python repository, a...
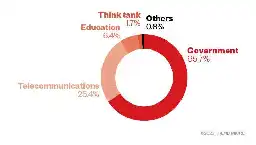
- Uncovering a New Activity Group Targeting Governments in the Middle East and Africa - Palo Alto Networks Blogwww.paloaltonetworks.com Through the Cortex XDR Lens: Uncovering a New Activity Group Targeting Governments in the Middle East and Africa - Palo Alto Networks Blog
This blog is about a new activity group that was observed targeting governments in the Middle East and Africa with some rare TTPs.
- Resident Campaignwww.esentire.com eSentire Threat Intelligence Malware Analysis: Resident Campaign
Learn about the Resident campaign and the threat actor's use of Rhamadanthys stealer in this malware analysis from Threat Response Unit (TRU).
- The Experience of Cybercrime in Georgia: Awareness, Victimisation and Reportingrusi.org The Experience of Cybercrime in Georgia: Awareness, Victimisation and Reporting
This paper establishes an independent evidence base on the experience and perception of cybercrime and online harms in Georgia, with a focus on how and why certain groups are more vulnerable.
- DoNot APT Elevates its Tactics by Deploying Malicious Android Apps on Google Play Storewww.cyfirma.com DoNot APT Elevates its Tactics by Deploying Malicious Android Apps on Google Play Store - CYFIRMA
EXECUTIVE SUMMARY The team at CYFIRMA recently obtained suspicious Android apps hosted on the Google Play Store under the account...
- China calls hacking report 'far-fetched' and accuses the US of targeting the cybersecurity industryapnews.com China calls hacking report 'far-fetched' and accuses the US of targeting the cybersecurity industry
China's government has rejected as “far-fetched and unprofessional” a report by a U.S. security firm that blamed Chinese-linked hackers for attacks on hundreds of public agencies, schools and other targets around the world.

- Swing VPN app is a DDOS botnetlecromee.github.io Swing VPN app is a DDOS botnet
tldr: Swing VPN is using its user base to DDOS sites using its users as a an attack botnet. Introduction It all started with a friend of mine complaining that his phone was doing a request to a specific app every few seconds. Initial assumption was that the phone was infected with a virus but a 2 mi...
- Case Study: cracking a global Adversary-In-The-Middle campaign using a threat intelligence toolkitblog.sygnia.co Case Study: cracking a global Adversary-In-The-Middle campaign using a threat intelligence toolkit
Using a variety of CTI enrichment techniques Sygnia was able to determine that the BEC attack was only a part of a much wider campaign, potentially impacting dozens of world-wide organizations.

- Automating acquisition for incident responsefalconforce.nl FalconFriday — Automating acquisition for incident response — 0xFF23 - FalconForce
What role can automation play in evidence collection in cyber incident response? We discuss possibilities in Azure and introduce ParrotForce.

- Security Threat Insights Report Q1 2023 - notable malware campaigns, trends and techniques identified from customer telemetry in calendar Q1 2023threatresearch.ext.hp.com HP Wolf Security Threat Insights Report Q1 2023 | HP Wolf Security
Don’t let cyber threats get the best of you. Read the HP Wolf Security Threat Insights Report for Q4 2022 to learn more about cyber threats and cyber security.

- Shampoo: A New ChromeLoader Campaignthreatresearch.ext.hp.com Shampoo: A New ChromeLoader Campaign | HP Wolf Security
Don’t let cyber threats get the best of you. Read our post, Shampoo: A New ChromeLoader Campaign, to learn more about cyber threats and cyber security.

- OnlyDcRatFans: Malware Distributed Using Explicit Lures of OnlyFans Pages and Other Adult Contentwww.esentire.com OnlyDcRatFans: Malware Distributed Using Explicit Lures of OnlyFans…
Learn more about the DcRAT malware and get security recommendations from our Threat Response Unit (TRU) to protect your business from this cyber threat.

- Cyber attack by group UAC-0057 (GhostWriter) against the state organization of Ukraine using PicassoLoader and Cobalt Strike Beacon (CERT-UA#6852) - use Chrome translatecert.gov.ua CERT-UA
Урядова команда реагування на комп’ютерні надзвичайні події України, яка функціонує в складі Державної служби спеціального зв’язку та захисту інформації України.

- Evasive File Smuggling with Skyhookwww.blackhillsinfosec.com Evasive File Smuggling with Skyhook - Black Hills Information Security
ImposterKeanu // Introduction This blog post introduces the reader to “The Obfuscation Hustle”, a term I enjoy using to describe the tedious process of obfuscating and delivering files to corporate […]
- Threat activity and vulnerabilities in Indonesia, Malaysia, Philippines, and Thailand | APNIC Blogblog.apnic.net Threat activity and vulnerabilities in Indonesia, Malaysia, Philippines, and Thailand | APNIC Blog
Guest Post: Understanding the attack surface of ASEAN economies to better support them.

- Shuckworm: Inside Russia’s Relentless Cyber Campaign Against Ukrainesymantec-enterprise-blogs.security.com Shuckworm: Inside Russia’s Relentless Cyber Campaign Against Ukraine
Attackers heavily focused on acquiring military and security intelligence in order to support invading forces.

- Hijacking S3 Buckets: New Attack Techniquecheckmarx.com Hijacking S3 Buckets: New Attack Technique
Without altering a single line of code, attackers poisoned the NPM package “bignum” by hijacking the S3 bucket serving binaries necessary for its function and replacing them with malicious ones

- Russian National Arrested and Charged with Conspiring to Commit LockBit Ransomware Attacks Against U.S. and Foreign Businesseswww.justice.gov Russian National Arrested and Charged with Conspiring to Commit LockBit Ransomware Attacks Against U.S. and Foreign Businesses
The Justice Department today announced charges against a Russian national for his involvement in deploying numerous LockBit ransomware and other cyberattacks against victim computer systems in the United States, Asia, Europe, and Africa.