Privacy
- Automakers Sold Driver Data for Pennies, Senators Saywww.nytimes.com Automakers Sold Driver Data for Pennies, Senators Say
Ron Wyden and Edward Markey urged the F.T.C. to investigate how car companies handled the data from millions of car owners.

https://archive.is/tc2xB
- X Training Grok AI On Tweets Without Notifying Userswww.macrumors.com X Training Grok AI On Tweets Without Notifying Users
Social network X (formerly Twitter) recently activated a setting that gives it permission to train Grok AI on user tweets. All X users are opted in...

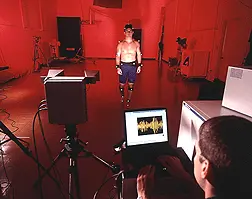
- Gait Recognition Technology
Gait biometric systems capture step patterns using video images and then convert the collated data into a mathematical equation. Gait as a biometric measure can be influenced by several factors, including footwear, terrain, fatigue, and injury.
...Love this sub, I don't have hardcore needs in terms of privacy, but wanted to know for people that enjoy a covid mask, their opinion on Gait Rec. Technologies, and does any one have any intel in throwing these systems off, whether or not that is impossible?
- Thoughts on Everdo? (todo app)everdo.net Everdo
Everdo is the best cross-platform todo list and Getting Things Done app. For Windows, Linux, Mac.
I've been using Microsoft todo for a good while now after failing to find any decent private todo tools some while back. To my disappointment, there seems to be nothing much, perhaps with this one exception.
Everdo is one I recently ran into. It is focused on a the “Getting Things Done” Methodology, but if you are uninterested in that you could presumably ignore the extraneous stuff. It offers a local-network sync (pretty unique) as well a hosted E2EE (if I read it correctly) cloud sync service. You can see more here https://help.everdo.net/docs/sync
Privacy policy seems fine https://everdo.net/legal/#privacy-policy
It is local first, albeit on some internal database, not local files
- Separate 2FA OTP app from my password manager
Do you think it's worth keeping 2FA OTPs in a separate source from your password manager? Currently I keep them in Bitwarden. I was thinking keeping them separate could add a little extra security in case my BW was cracked, but not sure it's worth the hassle of loading a second app for logins.
Do you know of an app that does 2FAs as conveniently as Bitwarden, in that it has mobile apps, browser extension, etc that can all access the same vault?
here's one i came across from an awesome-selfhosted list. i would need to test the PWA experience https://github.com/Bubka/2FAuth
- (Solved) How Does YouTube Know Where I Left Off On A Video?

Yesterday, I started watching a video on YouTube but closed out of my browser (Firefox) only a few minutes into the video.
I've got my Firefox set to delete all cookies, history, form data, etc on every close. (Pretty much everything but bookmarks.) The image on this post is a screenshot of my relevant settings.
Today, after having exited my browser and fully shut down my computer for a while, I remembered the video and decided to continue watching it.
In Firefox, I searched for the video (I used the search term "gnu taler" -- something worth looking into especially for folks interested in this particular Lemmy community by the way). In the search results, the video I was searching for showed the red bar at the bottom indicating I'd watched only the first few minutes of it.
Which seems weird given that I'd cleared all my browser data since I watched the first few minutes.
So I did some experimentation. I closed my browser completely again and opened it back up, searched in YouTube, and it still had the indicator. I updated to the latest version of Firefox in the Arch package repository. Same indicator. I tried the same in Chromium (which I've also got set to delete all browser data on close). Still the indicator. I installed Tor Browser Bundle (specifically torbrowser-launcher on Arch Linux), changed none of the default settings at all, and searched in YouTube. The indicator is present. In Tor Browser Bundle.
W
T
F
?
Anybody have any idea how that's possible?
My only guesses are:
- That search is so niche as to be literally unique (which if true makes me sad -- I really hope GNU Taler takes off and becomes widespread) and YouTube is using that to identify me.
- YouTube doesn't know where I left off at all. Not even my browser knows (because if it was my browser keeping track, it wouldn't persist between browsers). It's something else on my system that my browsers depend on or tap into.
The only other pieces of relevant info I can think to share:
- There's another video (also about GNU Taler) that I watched all the way through the same day that I started the video this post is about. It doesn't show any indicator.
- I tried searching on my phone's browser. No indicator. But then I'm not sure my phone ever shows indicators. I haven't tried this on any other devices on my network or anything.
- I still haven't watched the video in question. Heh.
Thanks in advance for any insight you might have.
Edit: Sorry for neglecting to mention previously that at no point during any of the above did I log in to YouTube. And the "Sign in" button was visible at the top of the page indicating I wasn't logged in. Since multiple people asked, I figured I should edit my OP with that info.
Edit2: Two more things to mention. I think some folks are thinking I copied the link and pasted it between browsers during the above test or something? The only reason the timestamp is included in the link I posted above is because when I copied it into this post, I didn't think to remove the timestamp. But I didn't do anything like copying the link from the search results in one browser and then paste the link into TBB or anything. In each separate browser, immediately after opening the browser, I went to YouTube (by typing "youtube.com<enter>" into the address bar) and put "gnu taler" into the search bar and hit enter. And in each browser, YouTube somehow remembered where I'd left off in a whole different browser -- with a different IP address in the case of the switch from Chromium to TBB. And no urls were copied between browsers in any of the above.
The other thing to mention. Changing my search term to the full title of the video ("Building an Open Source Payment System - Sebastian Javier Marchano, Taler System" sans quotes) gives the relevant video as the top search result, but no "left off" indicator. And I'm in the Firefox in which I first noticed it had remembered.
Oh, actually, one more thing to mention. After posting this, I continued watching. I'm probably about 3/4 done with it now. But I closed my browser again before completing it, reopened my browser, and searched "gnu taler". It gives the indicator, but the position of the indicator is roughly (possibly exactly) where it was when I first noticed it had remembered. Not where I left off after watching to roughly the 3/4 mark.
Edit3: Wow! Ok. I'm 99% sure folks smarter than me have hit upon what's going on here. Thanks in particular to Tony N and Chozo for the right answer. It looks like YouTube has a feature where, depending on your search terms, it may automatically skip you a certain ways into the video. (Like "oh, you searched for 'gnu taler'? Well, in this video result, this bit in the middle is the part that's relevant to your search terms, so we'll just start you such-and-such-many seconds into the video.") The red bar doesn't mean "you've watched this" at all. And YouTube isn't "remembering me" between browsers. It's just consistently (as long as I use the specific search terms "gnu taler") suggesting that I start that video 273 seconds in rather than from the beginning. And anyone who searches that exact search term should get similar results... unless they're on mobile for some weird reason? That paired with the coincidence that I'm pretty sure I just happened to have stopped the video yesterday right about at the same place where YouTube recommends you start had me very confused. Whatever the case, I'm satisfied this must be the right answer. Thanks again, ya'll!
- Anything wrong with using my real name in email aliases with organizations I have to communicate using my real identity anyway?
One example would be state disability programs, they already need my real name and identity to work with me. Are there any downsides to sharing a simplelogin alias containing my real name vs no containing my real name? I just think it would be easier record keeping for them.
- Meta Quest 3 - Privacy workaround?
Is there any up-to-date method to keep the Meta Quest 3 as privacy friendly as possilbe? I know it can't be made perfect, but maybe some known working block lists etc.?
i'm thinking about getting one but their data hoarding is the reason i don't want to. Unless i can somehow make it less invasive.
- Introducing Proton Wallet – a safer way to hold Bitcoinproton.me Introducing Proton Wallet – a safer way to hold Bitcoin | Proton
Proton Wallet is an easy-to-use self-custodial wallet that makes financial freedom attainable for everyone.

- How do I forward calls from JMP.chat number to SIM phone number?
Hello,
I want to buy a flip phone to reduce distractions and am planning on getting rid of my Pixel. I currently have Cheogram installed on my Pixel and want to forward calls/texts to my SIM phone number. I'm not sure if the current flip phones support Cheogram well (due to the small screen), that's mainly why I want to setup call forwarding.
Any help is appreciated.
- EU limits anonymous cash payments to €3k and all cash payments to €10k. Pirate party reacts.www.evz.de Cash payment: Cash limits in Europe
If you want to pay large sums of money abroad in the EU, for example when buying a car, there are a few rules you need to follow. This is because many EU countries have cash limits. This means that cash payments can only be made up to a certain amount.
cross-posted from: https://slrpnk.net/post/11683880
> cross-posted from: https://slrpnk.net/post/11683421 > > > The EU has quietly imposed cash limits EU-wide: > > * €3k limit on anonymous payments > > * €10k limit regardless (link which also lists state-by-state limits). > > > > From the jailed¹ article: > > > > > An EU-wide maximum limit of €10 000 is set for cash payments, which will make it harder for criminals to launder dirty money. > > > > It will also strip dignity and autonomy from non-criminal adults, you nannying assholes! > > > > > In addition, according to the provisional agreement, obliged entities will need to identify and verify the identity of a person who carries out an occasional transaction in cash between €3 000 and €10 000. > > > > The hunt for “money launderers” and “terrorists” is not likely meaningfully facilitated by depriving the privacy of people involved in small €3k transactions. It’s a bogus excuse for empowering a police surveillance state. It’s a shame how quietly this apparently happened. No news or chatter about it. > > > > ¹ the EU’s own website is an exclusive privacy-abusing Cloudflare site inaccessible several demographics of people. Sad that we need to rely on the website of a US library to get equitable access to official EU communication. > > > > update > > --- > > The Pirate party’s reaction is spot on. They also point out that cryptocurrency is affected. Which in the end amounts to forced banking. > > > > #warOnCash
- Basically, a good way to never trust "it's okay, the data is anonymized" again is simply knowing what the "Hemisphere Program" is.mastodon.social mcc (@mcc@mastodon.social)
Attached: 1 image Basically, a good way to never trust "it's okay, the data is anonymized" again is simply knowing what the "Hemisphere Program" is. https://www.eff.org/cases/hemisphere In short, the US government got access to number from, number to, datetime, length and sometimes location infor...
- FTC Issues Orders to Eight Companies Seeking Information on Surveillance Pricingwww.ftc.gov FTC Issues Orders to Eight Companies Seeking Information on Surveillance Pricing
The Federal Trade Commission issued orders to eight companies offering surveillance pricing products and services that incorporate data about consumers’ characteristics and behavior.

After reading such news I have an obvious question. Does anyone know a PayPal-like service, that allows to hide the destination of my transactions from Mastercard / bank, but with a good privacy policy? Or how else can I restrict the usage of my financial data by mastercard or bank?
- [Question] YouTube frontend with algorithm?
I’ve been using invidious for a few years. I recently changed up my morning routine and have been eating breakfast watching YouTube via the TV app versus on my PC.
It made me realize I kind of miss the recommended videos in some circumstances like when I just wanna veg out.
Are there any current viable yt front ends that either maintain the algorithm or utilize their own to find you new content?
- forced to buy an echo for new house. any suggestions?
my family is moving into a much bigger house than we used to have. we use amazon echos as an intercom system through the announcement feature. because our house is bigger, i’m being forced to get one myself for my room. i haven’t needed one for years because i use their app on my phone and i can see their announcements as a notification and i can also kill off most of its tracking by DNS. unfortunately my parents don’t understand this and are forcing me to get one. what can i do to limit its tracking?
- UN Cybercrime Draft Convention Dangerously Expands State Surveillance Powers Without Robust Privacy, Data Protection Safeguardswww.eff.org UN Cybercrime Draft Convention Dangerously Expands State Surveillance Powers Without Robust Privacy, Data Protection Safeguards
This is the third post in a series highlighting flaws in the proposed UN Cybercrime Convention. Check out Part I, our detailed analysis on the criminalization of security research activities, and Part II, an analysis of the human rights safeguards.As we near the final negotiating session for the...

- Global IT outage shows dangers of cashless society, campaigners saywww.theguardian.com Global IT outage shows dangers of cashless society, campaigners say
Cash provides essential fallback when digital payments break down, Payment Choice Alliance points out

- Best Voice-over-IP Providers in 2024blog.thenewoil.org Best Voice-over-IP Providers in 2024
There are many ways to describe Voice-over-IP, or VoIP. I've seen it called an anonymous, internet, alias, or throwaway phone number (and...

> There are many ways to describe Voice-over-IP, or VoIP. I've seen it called an anonymous, internet, alias, or throwaway phone number (and more). Regardless of the name, I personally consider VoIP to be a healthy part of a good privacy and security strategy. The advantages are endless. For one, VoIP is harder to SIM Swap compared to a normal SIM phone number. VoIP can also help provide you privacy since most SIM numbers can easily be Googled or looked up on any number of the hundreds of people search sites and return information about the carrier and who the number is registered to. On the day-to-day, VoIP – combined with other strategies I recommend on The New Oil – can help reduce spam calls/texts, prevent would-be stalkers, create healthy work/life balances, control what information people (like prospective employers) can find about you, and help compartmentalize or reduce tracking by big corporations. Sadly, VoIP is a tool that's not widely available in many countries, but for those with access to it, VoIP can provide numerous benefits and should at very least be considered. So this week let's explore some of the best VoIP options currently available for consumers.
- Alternative to GrapheneOS
Im considering buying a new phone and i don't really consider a Pixel. I really like Fairphones approach, with the self repairable stuff. Even though they don‘t have a headphone jack. But well… I can’t change it. I’ll definitely go with the adapter over wireless headphones.
But to my question: What private OSes are there? Fairphone sells FP4s with eOS, how is that? And does it work on the FP5? GrapheneOS only works on Google Pixels right?
- Traveling this summer? Maybe don’t let the airport scan your face.www.vox.com Traveling this summer? Maybe don’t let the airport scan your face.
You have the right to opt out of facial recognition tech. Here’s how.

- Protecting your privacy while participating in activismwww.eff.org Beyond Pride Month: Protecting Digital Identities For LGBTQ+ People
The internet provides people space to build communities, shed light on injustices, and acquire vital knowledge that might not otherwise be available. And for LGBTQ+ individuals, digital spaces enable people that are not yet out to engage with their gender and sexual orientation.

Tips to keeping your identity secure, and protecting other members of your community from being accidentally doxxed or forced offline.
Extremely useful, especially for people who coordinate larger protests or online communities.
- Private location sharing alt to life360github.com GitHub - Myzel394/locus: Share your location end-to-end encrypted on decentralized servers using Nostr.
Share your location end-to-end encrypted on decentralized servers using Nostr. - Myzel394/locus

Ive been on the hunt for a while for something like this. I started looking again since the life360 breach. This is nearly perfect. Just need the iOS app to have a little more support and be in the app store for my less techy friends/family.
- My Privacy Setup
Hi! 2 and 4 months ago @Hellfire103 and @Charger8232 made a post about their privacy setup. So I though I would also share mine.
Remember these rules:
-
Be respectful! Some people are early on in their privacy journey, or have a lax threat model. Just because it doesn’t align with yours, or uses some anti-privacy software, doesn’t mean you can downvote them! Help them improve by giving suggestions on alternatives.
-
Don’t promote proprietary software! Proprietary software, no matter how good it may seem, is against the community rules, and generally frowned upon. If you aren’t sure, you can always ask! This is a place to learn. Don’t downvote people just because they don’t know!
-** Don’t focus solely on me!** I want to mention that this thread is not designed to pick apart only my setup. The point is to contribute your own and help others. That doesn’t mean you can’t still give suggestions for mine, but don’t prioritize mine over another.
- Be polite! This falls under “Be respectful”, but be kind to everyone! Say please, thank you, and sorry. Lemmy is really good about this, but there will always be someone.
Here is my setup:
Web browsing
- I use Librewolf for almost everything.
- For 3D stuff (games, 3d modelling) I use Brave.
- On mobile I use Vanadium.
- My preferred search engine is Kagi.
- Most if the time I have MullvadVPN enabled.
Desktop and laptop
- I have self-build Ryzen + Radeon PC and Ideapad with Ryzen CPU.
- I use Arch Linux BTW!
- I have disk encryption and Nitrokey as a decryption key (or a long password of course).
- I have secure boot with locked BIOS.
- I'm running self-compiled linux-hardened kernel.
- I'm using Gnome (Wayland).
- I have only open-source apps installed.
Mobile
- I have Google Pixel 7a with GrapheneOS.
- I have different 5 profiles: main, google, school, finance, anonymous.
- I have PIN on every profile and also fingerprint for main and school profiles.
- I always use VPN, either Mullvad or self-hosted Wireguard.
- I don’t use a privacy screen protector (for now).
Messenger
- Signal for my family.
- Viber for my schoolmates.
- MS Teams for school.
- Matrix for help with some open-source projects.
- Discord for voice chat and local scouts group. I have Aliucord on mobile and Armcord on desktop.
Online accounts
- Passwords are safe in self-hosted Bitwarden (Vaultwarden).
- I use 2FA if I can. Either hardware 2FA - Nitrokey, or TOTP with Aegis.
- I use SimpleLogin for email aliases and randomly generated usernames and passwords.
Video streaming
- I watch only Youtube. Newpipe on mobile and Invidious on desktop.
AI
- I do not use AI a lot, but if I do I use locally running LLama3 8B or Duckduckgo's LLama3 70B
Social Media
- I had Instagram, Snapchat and Viber accounts, but I've deleted them.
- I use only Lemmy on clearweb and Dread on darkweb.
- I have Mastodon account, but I don't use it.
Email
- I use ProtonMail.
- One of the best privacy things you can do is use SimpleLogin (or other email alias service).
Shopping/Finance
- IRL I use cash most of the time.
- Online I use Monero if I can, otherwise just my credit card.
- Cashew app for helping managing my purchases.
Music streaming
- I use only RiMusic on my phone, that's it.
TV shows
- I use a VPN, that's all I'm gonna say...
Gaming
- Minecraft, Veloren, SuperTuxKart, and some Steam games.
Programming
- I forgot how to code in Python, because Rust is so much better.
- VS Codium.
Productivity
- LibreOffice for simple stuff.
- Typst for proper documents.
Paid services
- ProtonMail - 4$ per month
- SimpleLogin - 30$ per year
- MullvadVPN - 5$ per month
- Kagi - 10$ per month. For 5$ you get 300 searches, I use ~350 searches so I will try to lower my searches.
- Domain - 13$ per year
Self-hosted
- Everything runs on Raspberry Pi 4 with encrypted micro SD card.
- Pi-Hole for blocking ads on network level.
- Bitwarden (Vaultwarden) for storing all my passwords.
- Wireguard server (with pihole as DNS) for connecting back home from anywhere.
- Ntfy for self-hosted push notifications.
- MollySocket for Signal push notifications.
- FindMyDevice if I lost my phone.
- Cloudflare DDNS, because I don't have static IP.
- Nginx Proxy Manager.
- Watchtower automatically updates docker containers.
- My website.
Misc
- I have Samsung Galaxy Watch 4 classic. I'm trying to do something about it...
- I'm using Syncthing to sync documents and pictures between my devices.
- I don't have a car (because I can't - I'm 17) and I won't have one for quite some time. I have a bicycle and my parents have 2 (smart/spy) cars.
- I'm into crypto (mostly XMR) and I'm trading a little (making a trading bot) on MEXC. I also have Ledger Nano S Plus.
- I have a 3d printer and it's fun and usefull :)
TODO
- self-host Git repos for my projects.
- Buy a privacy screen protector when I break my current one.
- Buy a faraday bag, just in case.
- Do something about my spywatch (maybe sell).
- Make backups... Yep, I don't have any yet.
- Monitor and harden all my devices.
- Memorize cryptowallet's private key in case it gets lost.
Thanks for reading!
-
- A tip for Android users.
I just wanted to share that you can disable google play store on stock Android and not lose that much functionality, if for any reason you use an app that require Google play store or you want to make a play store purchase, you can enable it again.
I personally disabled it and I get my apps from Aurora Store, ApkPure and Droidify.
It decreased my phone battery usage by a lot and I am less dependent on google overall.
- Leaked Docs Show What Phones Cellebrite Can (and Can’t) Unlockwww.404media.co Leaked Docs Show What Phones Cellebrite Can (and Can’t) Unlock
The leaked April 2024 documents, obtained and verified by 404 Media, show Cellebrite could not unlock a large chunk of modern iPhones.

> ##### Leaked Docs Show What Phones Cellebrite Can (and Can’t) Unlock > > The leaked April 2024 documents, obtained and verified by 404 Media, show Cellebrite could not unlock a large chunk of modern iPhones. > > Cellebrite, the well-known mobile forensics company, was unable to unlock a sizable chunk of modern iPhones available on the market as of April 2024, according to leaked documents verified by 404 Media. > > The documents, which also show what various Android handsets and operating system versions Cellebrite can access, provide granular insight into the very recent state of mobile forensic technology. Mobile forensics companies typically do not release details on what specific models their tools can or cannot penetrate, instead using vague terms in marketing materials. The documents obtained by 404 Media, which are given to customers but not published publicly, show how fluid and fast moving the success, or failure, of mobile forensic tools can be, and highlights the constant cat and mouse game between hardware and operating manufacturers like Apple and Google, and the hacking companies looking for vulnerabilities to exploit. > > Analysis of the documents also comes after the FBI announced it had successfully gained access to the mobile phone used by Thomas Matthew Crooks, the suspected shooter in the attempted assassination of former President Donald Trump. The FBI has not released details on what brand of phone Crooks used, and it has not said how it was able to unlock his phone. > > The documents are titled “Cellebrite iOS Support Matrix” and “Cellebrite Android Support Matrix” respectively. An anonymous source recently sent the full PDFs to 404 Media, who said they obtained them from a Cellebrite customer. GrapheneOS, a privacy and security focused Android-based operating system, previously published screenshots of the same documents online in May, but the material did not receive wider attention beyond the mobile forensics community. > > For all locked iPhones able to run 17.4 or newer, the Cellebrite document says “In Research,” meaning they cannot necessarily be unlocked with Cellebrite’s tools. For previous iterations of iOS 17, stretching from 17.1 to 17.3.1, Cellebrite says it does support the iPhone XR and iPhone 11 series. Specifically, the document says Cellebrite recently added support to those models for its Supersonic BF [brute force] capability, which claims to gain access to phones quickly. But for the iPhone 12 and up running those operating systems, Cellebrite says support is “Coming soon.” > > > A SECTION OF THE IOS DOCUMENT. IMAGE: 404 MEDIA. > > The iPhone 11 was released in 2019. The iPhone 12 was launched the following year. In other words, Cellebrite was only able to unlock iPhones running the penultimate version of iOS that were released nearly five years ago. > > The most recent version of iOS in April 2024 was 17.4.1, which was released in March 2024. Apple then released 17.5.1 in May. According to Apple’s own publicly released data from June, the vast majority of iPhone users have upgraded to iOS 17, with the operating system being installed on 77 percent of all iPhones, and 87 percent of iPhones introduced in the last four years. The data does not break what percentage of those users are on each iteration of iOS 17, though. > > Cellebrite offers a variety of mobile forensics tools. That includes the UFED, a hardware device that can extract data from a physically connected mobile phone. The UFED is a common sight in police departments across the country and world, and is sometimes used outside of law enforcement too. Cellebrite also sells Cellebrite Premium, a service that either gives the client’s UFED more capabilities, is handled in Cellebrite’s own cloud, or comes as an “offline turnkey solution,” according to a video on Cellebrite’s website. > > That video says that Cellebrite Premium is capable of obtaining the passcode for “nearly all of today’s mobile devices, including the latest iOS and Android versions.” > > That claim does not appear to be reflected in the leaked documents, which show that, as of April, Cellebrite could not access from locked iOS phones running 17.4. > > The second document shows that Cellebrite does not have blanket coverage of locked Android devices either, although it covers most of those listed. Cellebrite cannot, for example, brute force a Google Pixel 6, 7, or 8 that has been turned off to get the users’ data, according to the document. The most recent version of Android at the time of the Cellebrite documents was Android 14, released October 2023. The Pixel 6 was released in 2021. > > > A SECTION OF THE ANDROID DOCUMENT. IMAGE: 404 MEDIA. > > Cellebrite confirmed the authenticity of the documents in an emailed statement to 404 Media. “Similar to any other software company, the documents are designed to help our customers understand Cellebrite’s technology capabilities as they conduct ethical, legally sanctioned investigations—bound by the confines of a search warrant or an owner’s consent to search. The reason we do not openly advertise our updates is so that bad actors are not privy to information that could further their criminal activity,” Victor Ryan Cooper, senior director of corporate communications and content at Cellebrite, wrote. > > “Cellebrite does not sell to countries sanctioned by the U.S., EU, UK or Israeli governments or those on the Financial Action Task Force (FATF) blacklist. We only work with and pursue customers who we believe will act lawfully and not in a manner incompatible with privacy rights or human rights,” the email added. In 2021 Al Jazeera and Haaretz reported that a paramilitary force in Bangladesh was trained to use Cellebrite’s technology. > > Cellebrite is not the only mobile forensics company targeting iOS devices. Grayshift makes a product called the GrayKey, which originally was focused on iOS devices before expanding to Android phones too. It is not clear what the GrayKey’s current capabilities are. Magnet Forensics, which merged with Grayshift in 2023, did not immediately respond to a request for comment. > > Cellebrite’s Android-focused document also explicitly mentions GrapheneOS in two tables. As well as being an operating system that the privacy-conscious might use, 404 Media has spoken to multiple people in the underground industry selling secure phones to drug traffickers who said some of their clients have moved to using GrapheneOS in recent years. > > Daniel Micay, founder of GrapheneOS, told 404 Media that GrapheneOS joined a Discord server whose members include law enforcement officials and which is dedicated to discussions around mobile forensics. “We joined and they approved us, with our official GrapheneOS account, but it seems some cops got really mad and got a mod to ban us even though we didn't post anything off topic or do anything bad,” Micay said. > > There is intense secrecy around the community of mobile forensics experts that discuss the latest unlocking tricks and shortcomings with their peers. In 2018 at Motherboard, I reported that law enforcement officials were trying to hide their emails about phone unlocking tools. At the time, I was receiving leaks of emails and documents from inside mobile forensics groups. In an attempt to obtain more information, I sent public records requests for more emails. > > “Just a heads up, my department received two public records request[s] from a Joseph Cox at Motherboard.com requesting 2 years of my emails,” a law enforcement official wrote in one email to other members. I learned of this through a subsequent leak of that email. (404 Media continues to receive leaks, including a recent set of screenshots from a mobile forensics Discord group). > > Google did not respond to a request for comment. Apple declined to comment.
- [Question] Font fingerprinting -- even tor browser is vulnerable!?

I've just been playing around with https://browserleaks.com/fonts . It seems no web browser provides adequate protection for this method of fingerprinting -- in both brave and librewolf the tool detects rather unique fonts that I have installed on my system, such as "IBM Plex" and "UD Digi Kyokasho" -- almost certainly a unique fingerprint. Tor browser does slightly better as it does not divulge these "weird" fonts. However, it still reveals that the google Noto fonts are installed, which is by far not universal -- on a different machine, where no Noto fonts are installed, the tool does not report them.
For extra context: I've tested under Linux with native tor browser and flatpak'd Brave and Librewolf.
What can we do to protect ourselves from this method of fingerprinting? And why are all of these privacy-focused browsers vulnerable to it? Is work being done to mitigate this?
- Can data removal services be trusted?
What is the general consensus on trusting data removal services with the data you provide them?
I’ve spent 5 years telling myself I’ll go through the long lists of data aggregators and one by one manually send removal requests. But it’s such a massive undertaking. I’d like to finally get it done through one of these services, but my gut tells me it feels wrong.
Has anybody used them and how do you feel about it? Is DeleteMe a good choice?
- Proton just joined the AI clown car showproton.me Introducing Proton Scribe, a private writing assistant that writes and proofreads emails for you | Proton
With Proton Scribe, your team will save time writing emails, and you'll protect your business data by reducing the need to expose it to AI assistants.

Fuck this shit, why does every fucking thing need an LLM?
- Adversarial images on clothing to combat AI facial recognition without covering the facepetapixel.com This Clothing Line Tricks AI Cameras Without Covering Your Face
An AI camera may think you're a zebra.

- How a little-known tool is sweeping the real estate industry by giving instant access to vast amounts of homebuyer datatherecord.media How a little-known tool is sweeping the real estate industry by giving instant access to vast amounts of homebuyer data
When Florida real estate professional Susan Hicks discovered the app Forewarn over a year ago, she was shocked to learn that for a service costing about $20 a month she could instantaneously retrieve detailed data on prospective clients with only their phone number.

- Hypatia FOSS anti malware app.
Anyone have any experience with this app? Could it be malware? Are there other Foss or FLOSS alternatives?
- If you use Simplelogin with your iCloud email, how has your mileage been?
I just tried changing my email on studentaid.gov to a simplelogin alias (using SL is a habit at this point) and I got notifications that emails from it were bounced while trying to verify the email change with sent codes. I looked it up and found a bunch of Reddit posts about issues with SL and iCloud.
- What do you folks do for IRL privacy in terms of CCTV, facial recognition, etc?
Digital privacy seems quite straightforward, because your digital devices are environments you more or less can have complete control over if you want to. But when you're out and about, it's a much more uncontrolled environment. There are cameras everywhere.
I wear face masks everywhere for a combo of protecting myself from illness and privacy. But the limitation is social acceptability. If anything good came out of covid it's the normalisation of face masks, but you are far from unidentifiable if your only face covering is a covid mask. We're lucky that sunglasses and hoodies on their own are fairly normal, but all of the above in combination would draw attention to you. And it's definitely not socially acceptable to walk around in a balaclava.
The other thing is forensic data. If you don't wear gloves, you'll leave fingerprints everywhere, and hair too. I suppose wearing gloves is not particularly seen as weird or suspicious, but it just seems like there are a lot of considerations and challenges with preventing the state from knowing your every move when you leave the house.
What considerations do you make for IRL privacy, if any?
(Not particularly interested in "I don't care about IRL privacy so I don't do anything"—that's fine and your choice, but ofc this question is aimed towards those who do care)
- Alternatives to Google Maps' timeline feature on iOS?
I want to keep a timeline of the places I go like Google Maps can, and export it to mac for my diary*. The maps app doesn't have to be great, it just needs to keep a timeline in the background, I would still use Apple Maps as my main navigation app.
*(ideally I can automatically export it somehow, perhaps with the Shortcuts and Scriptable app but just tell me any apps with a timeline and export feature)
- I2P 2.6.0 Release - Blog - I2P
cross-posted from: https://lemmy.world/post/17746311
> This release, I2P 2.6.0, continues our work by fixing bugs, adding features, and improving the network's reliability. > > Newer routers will be favored when selecting floodfill routers. I2PSnark received features which improve the performance of PeX(Peer Exchange), in addition to bug fixes. Legacy transport protocols are being removed, simplifying the code in the UDP transports. Locally-hosted destination will be reachable by local clients without requesting their LeaseSet, improving performance and testability. Additional tweaks were made to peer selection strategies. > > I2P no longer allows I2P-over-Tor, connections from Tor exit IP addresses are now blocked. We discourage this because it degrades the performance of I2P and uses up the resources of Tor exits for no benefit. If you are a helpful person running both a Tor Exit and I2P we encourage you to continue to do so, using different IP addresses for each. Non-exit relays and Tor clients are unaffected by this and do not need to change anything. > > As usual, we recommend that you update to this release. The best way to maintain security and help the network is to run the latest release. > > RELEASE DETAILS > Changes > > * Router: Increase minimum version for floodfill routers > > * Router: Disable I2P over Tor > > * Address Book: Cache locally hosted destinations > > Bug Fixes > > * I2PSnark: Peer Exchange Tweaks > > * I2PSnark: Bugfixes > > * Router: Peer Selection Tweaks > > Other > > * Translation updates
- Use Galaxy Watch without Google?
I have Galaxy Watch 4 and Pixel with GrapheneOS. Currently I have second profile with galaxy wearable and google play services for connecting to the watch. Before I've installed graphene I was using my watch as any other person, for notifications, sports, etc. Now I use it only for checking what time is it and developing apps. I can see my sports activity only for a week back, because samsung health only works on main profile.
Is there a way for me to use my watch on main profile without google and samsung apps? Maybe with some alternative app? Or should I sold my watch and buy a new one? I've heard good things about garmin and polaris? I would love option to develop my own apps on them.
- Techlore - Unsubscribe
After their shameless Synology shilling a couple of weeks ago, today Techlore is trying to sell me Proton Pass.
Is Proton Pass a bad password manager? I don't know. It seems okay, but I have no opinion.
What I do know is that Techlore is affiliated with Proton, which makes their newest 10-minute video - in which they reveal the affiliation only at the last minute - 10 minutes of my life I'll never get back.
Unfortunately, In the business they're in, the merest hint of a bias kind of invalidates any advice they give. As the saying goes, when you point out other people's body odor, you'd better make sure you took a shower yourself.
Unsubscribe...
- WebRTC IP Leaking
i want to understand more about WebRTC security when using vpn. id like to know if it is more secure with VPN than without… or even if its recommended to use WebRTC with VPN.
i created a webrtc demo: https://chat.positive-intentions.com/#/webrtc (the corresponding code its created with: https://github.com/positive-intentions/chat/blob/staging/src/components/pages/webrtc/WebRTC.jsx)
if i generate a “WebRTC offer” then i see a bunch of information including my IP address.
if i do the same with VPN, i see that my ip address isnt in that payload.
following the information here: https://thehackernews.com/2015/02/webrtc-leaks-vpn-ip-address.html?m=1
and using the demo here: https://ipleak.net/
it seems even with vpn, the local ISP ip seems detected.
a recurring concern ive had on reddit about the security of my app is that webrtc exposes ip addresses. im investigating using the app with vpn. it seems to work like normal.
in the example details given above, i see while the local ISP IP is exposed, the personal ip address is still hidden. im sure what is exposed there is not worthless, but it could help users with privacy and security.
on the back of this investigation id like to see if i can add something like a toggle in my app called “enforce VPN” which will first check to see if you are on a vpn, and if you are, open the rest of the app.
my app is using peerjs-server as the connection broker. this is a third party i have no contractual agreement to provide me with a service. it could help to hide your IP from this service.
- Is there a way to make it so that your devices (sd cards, USBs, phones, laptops) etc can't be copied without knowing the password ?
cross-posted from: https://programming.dev/post/17104927
> After the news about FBI accesing trump shooters phone some people are speculating that they copied the phone storage so that they could bruteforce it without getting locked out if that is true is there anyway to make it so that your digital device can't be copied without the passwd if someone has physical acess to it and all the bruteforcing etc have to be done on the original device itself so we have a better chance of privacy . I am a layman but i use a good enough password on my phone and encrypt some sd card storage (which i knoe can be copied bcause i do it myself) but if the phones whole storage can be copied it seems kinda pointless . so my questions are : > > > 1 Does new smartphones do it by default ?if so how is wiping the phone when forgetting password possible ? > > > 2 does full disk encryption do this ? > > > 3 Does windows (8) have any thing that could do this for micro sd card and smartphone ? (some background is i only have a windows 8 craptop and it takes ages to load and Microsoft appstore nor sideloading works now encrypting the laptop is not needed as i barely do anything on it but was thinking if i could encrypt my phone or sd card using it (it is really really slow (think can't even load MS word in an hour slow) ) if not see question 4 )also before you ask can't install linux tried and failed. > > > 4 beside from encrypting certain files using file manager encryption can i encrypt my sd card on android itself by using any app ? (preferably from fdroid ) . > > > 5 is all these even possible or is our only option hoping that our passwds are too complex to be bruteforced ?
> 6 also many people talk about updating your OS to increasing security but what about outdated hardware ? do they posses a risk or things like USB,sd cards etc which doesn't get any update ? Do they suffer security risk as time moves on ? is that even a thing ?
> > > Try to answer questions in these format pardon my ignorance and grammer even if i delete my acc feel free to still comment so it can be useful to others and i may still drop in to see the answers .
idk how crossposting works but i have also made this post on asklemmy .