Privacy
- Software with politic opinion is a security threatvitonsky.net Software with politic opinion is a security threat
The software that has a political opinion implies a bias and high risk for security. Avoid software with a "position" today, so you don't get hacked tomorrow.

- POC: Decentralized Chat
chat.positive-intentions.com
github.com/positive-intentions/chat
I'm excited to share with you an instant messaging application I've been working on that might interest you. This is a chat app designed to work within your browser, with a focus on browser-based security and decentralization.
What makes this app unique is that it doesn't rely on messaging servers to function. Instead, it works based on your browser's javascript capabilities.
Here are some features of the app:
- Encrypted messaging: Your messages are encrypted, making them more secure.
- File sharing: Easily share files using WebRTC technology and QR codes.
- Voice and video calls: Connect with others through voice and video calls.
- Shared virtual space: Explore a shared mixed-reality space.
- Image board: Browse and share images in a scrollable format.
Your security is a top priority. Here's how the app keeps you safe:
- Decentralized authentication: No central server is required for login, making it harder for anyone to gain unauthorized access.
- Unique IDs: Your ID is cryptographically random, adding an extra layer of security.
- End-to-end encryption: Your messages are encrypted from your device to the recipient's device, ensuring only you and the recipient can read them.
- Local data storage: Your data is stored only on your device, not on any external servers.
- Self-hostable: You have the option to host the app on your own server if you prefer.
A decentralized infrastructure has many unique challenges and this is a unique approach. Ive taken previous feedback and made updates. Its important to note, the app is an unstable proof-of-concept and a work-in-progress. Its important to understand at this early stage in the project, there will be breaking changes. It is not ready to replace any existing apps or services. While the app is aiming to be an encrypted and secure chat system, the project is not mature enough to have been reviewed by security professionals and should not be considered encrypted or secure. it is provided for testing/review/feedback purposes.
Looking forward to hearing your thoughts!
- Why Your Wi-Fi Router Doubles as an Apple AirTag – Krebs on Security
> Apple and the satellite-based broadband service Starlink each recently took steps to address new research into the potential security and privacy implications of how their services geo-locate devices. Researchers from the University of Maryland say they relied on publicly available data from Apple to track the location of billions of devices globally -- including non-Apple devices like Starlink systems -- and found they could use this data to monitor the destruction of Gaza, as well as the movements and in many cases identities of Russian and Ukrainian troops. At issue is the way that Apple collects and publicly shares information about the precise location of all Wi-Fi access points seen by its devices. Apple collects this location data to give Apple devices a crowdsourced, low-power alternative to constantly requesting global positioning system (GPS) coordinates.
> Both Apple and Google operate their own Wi-Fi-based Positioning Systems (WPS) that obtain certain hardware identifiers from all wireless access points that come within range of their mobile devices. Both record the Media Access Control (MAC) address that a Wi-FI access point uses, known as a Basic Service Set Identifier or BSSID. Periodically, Apple and Google mobile devices will forward their locations -- by querying GPS and/or by using cellular towers as landmarks -- along with any nearby BSSIDs. This combination of data allows Apple and Google devices to figure out where they are within a few feet or meters, and it's what allows your mobile phone to continue displaying your planned route even when the device can't get a fix on GPS.
> With Google's WPS, a wireless device submits a list of nearby Wi-Fi access point BSSIDs and their signal strengths -- via an application programming interface (API) request to Google -- whose WPS responds with the device's computed position. Google's WPS requires at least two BSSIDs to calculate a device's approximate position. Apple's WPS also accepts a list of nearby BSSIDs, but instead of computing the device's location based off the set of observed access points and their received signal strengths and then reporting that result to the user, Apple's API will return the geolocations of up to 400 hundred more BSSIDs that are nearby the one requested. It then uses approximately eight of those BSSIDs to work out the user's location based on known landmarks.
> In essence, Google's WPS computes the user's location and shares it with the device. Apple's WPS gives its devices a large enough amount of data about the location of known access points in the area that the devices can do that estimation on their own. That's according to two researchers at the University of Maryland, who theorized they could use the verbosity of Apple's API to map the movement of individual devices into and out of virtually any defined area of the world. The UMD pair said they spent a month early in their research continuously querying the API, asking it for the location of more than a billion BSSIDs generated at random. They learned that while only about three million of those randomly generated BSSIDs were known to Apple's Wi-Fi geolocation API, Apple also returned an additional 488 million BSSID locations already stored in its WPS from other lookups.>Apple and the satellite-based broadband service Starlink each recently took steps to address new research into the potential security and privacy implications of how their services geo-locate devices. Researchers from the University of Maryland say they relied on publicly available data from Apple to track the location of billions of devices globally — including non-Apple devices like Starlink systems — and found they could use this data to monitor the destruction of Gaza, as well as the movements and in many cases identities of Russian and Ukrainian troops.
"Plotting the locations returned by Apple's WPS between November 2022 and November 2023, Levin and Rye saw they had a near global view of the locations tied to more than two billion Wi-Fi access points," the report adds. "The map showed geolocated access points in nearly every corner of the globe, apart from almost the entirety of China, vast stretches of desert wilderness in central Australia and Africa, and deep in the rainforests of South America."
The researchers wrote: "We observe routers move between cities and countries, potentially representing their owner's relocation or a business transaction between an old and new owner. While there is not necessarily a 1-to-1 relationship between Wi-Fi routers and users, home routers typically only have several. If these users are vulnerable populations, such as those fleeing intimate partner violence or a stalker, their router simply being online can disclose their new location."
- Apple and Google deliver support for unwanted tracking alerts in iOS and Android
https://www.apple.com/newsroom/2024/05/apple-and-google-deliver-support-for-unwanted-tracking-alerts-in-ios-and-android/
- Genetic testing giant 23andMe is reportedly turning the blame back on its customers for its recent data breachwww.businessinsider.com Genetic testing giant 23andMe is reportedly turning the blame back on its customers for its recent data breach
23andMe shrugged off blame for its massive data breach, saying users "negligently" recycled and failed to update passwords, according to TechCrunch.
- Riot Games Now Requires Kernel-Level Anti-Cheat Software for League of Legends, Following Valorant's Implementationtuta.com Riot Requires Kernel Level Anti-Cheat Software
League of Legends and Valorant Players Being Forced to Run Closed Source Low-Level Software.

cross-posted from: https://lemmy.world/post/10958052
> Vanguard, the controversial anti-cheat software initially attached to Valorant, is now also coming to League of Legends. > > Summary: > > The article discusses Riot Games' requirement for players to install their Vanguard anti-cheat software, which runs at the kernel level, in order to play their games such as League of Legends and Valorant. The software aims to combat cheating by scanning for known vulnerabilities and blocking them, as well as monitoring for suspicious activity while the game is being played. However, the use of kernel-level software raises concerns about privacy and security, as it grants the company complete access to users' devices. > > The article highlights that Riot Games is owned by Tencent, a Chinese tech giant that has been involved in censorship and surveillance activities in China. This raises concerns that Vanguard could potentially be used for similar purposes, such as monitoring players' activity and restricting free speech in-game. > > Ultimately, the decision to install Vanguard rests with players, but the article urges caution and encourages players to consider the potential risks and implications before doing so.
- A year of surveillance in France: a short satirical tale by La Quadrature du Netvideo.lqdn.fr A year of surveillance in France: a short satirical tale by La Quadrature du Net
Fighting against surveillance has never been easy. But in the past year it has been specially tough in France. This talk is about shedding light on the many situations where the French State used surveillance to increase repression, mainly against activists, during the last months. Not to despair of...
Fighting against surveillance has never been easy. But in the past year it has been specially tough in France. This talk is about shedding light on the many situations where the French State used surveillance to increase repression, mainly against activists, during the last months. Not to despair of this, but willing to provide a sincere overview to the rest of the world, La Quadrature du Net proposes to depict this situation as a satirical tale, with its own characters, plots and suspense. We want to show the political tension going on right now in France and how the checks and balances are lacking to stop this headlong rush to a surveillance state.
Looking back to France in 2023, what do we see? Implementation of new technologies such as drones, DNA marking or new generation of spywares. Also, an intensification of political surveillance, either by law enforcement deploying disproportionate means of investigations towards environmental activists or intelligence services using cameras or GPS beacons to spy on places or people that they find too radical. It was also the year of the “8 December” case, a judicial case where among other things, encrypted communications of the prosecuted persons were considered as signs of "clandestinity" that reveal criminal intentions.
On top of this, we also had to deal with the legalization of biometric surveillance for the Olympics and massive censorship of social networks when riots erupted in suburbs against police violence.
This talk is about showing the reality of the situation at stake right now in France, and how it could influence the rest of Europe. At the end, we hope to raise awareness in the international community and start thinking about how, together, we can put pressure on a country who uses its old reputation to pretend to be respectful of human rights.
Source: https://media.ccc.de/v/37c3-12309-a_year_of_surveillance_in_france_a_short_satirical_tale_by_la_quadrature_du_net
French version: https://video.lqdn.fr/w/rXmBKD6NcfxWxJEPHUZc4Z
German version: https://video.lqdn.fr/w/315ZAQFMTMG7wqiMDdGvsi
- Indian journalists targeted by Israeli spyware again: What do we know?www.aljazeera.com Indian journalists targeted by Israeli spyware again: What do we know?
A forensic investigation reveals that the Pegasus software was recently used to target Indian journalists.

- 4-year campaign backdoored iPhones using possibly the most advanced exploit everarstechnica.com 4-year campaign backdoored iPhones using possibly the most advanced exploit ever
"Triangulation" infected dozens of iPhones belonging to employees of Moscow-based Kaspersky.

- Is Cloudflare snooping?
cross-posted from: https://links.hackliberty.org/post/609883
> This BBC interview has a #Cloudflare rep David Bellson who describes CF’s observations on internet traffic. CF tracks for example the popularity of Facebook vs. Tiktok. Neither of those services are Cloudflared, so how is CF tracking this? Apparently they are snooping on traffic that traverses their servers to record what people are talking about. Or is there a more legit way Cloudflare could be monitoring this activity?
- Naughty List of Tech Toys that Spy, Steal and Shock
This guide isn't a "what not to buy" list. It acknowledges that no internet-connected toy can be entirely child proof because tech companies have yet to prioritize children's safety in their designs.
- crude tracking technique - mailing letters just to see what bounces
Some banks will annually mail a paper “welcome” letter to all customers purely for the purpose of collecting bounced mail ultimately to verify if anyone has moved without telling them. The letters never state that’s the purpose.. they take that opportunity to talk about their service in arbitrary ways. Some banks even charge customers a fee for their cost in doing that. If you ask the banker about it they readily admit that it’s an address verification technique.
That’s it.. just a PSA so folks are aware, as it is a bit sneaky.
Some national postal services (e.g. USPS) sell your mail forwarding information which is how you get tracked to your new location by various entities even when you did not inform them of your new address. So obviously a good defensive measure is to never use the mail forwarding service. Select the entities you want to know your new address and inform them directly. But then to get some immunity to the sneaky trick in the 1st paragraph, perhaps give the next resident a stack of addressed envelopes and stamps and ask the next resident to
forward(remail) for you.. or just ask them to trash your mail instead of returning it. - Judge: Amazon “cannot claim shock” that bathroom spycams were used as advertisedarstechnica.com Judge: Amazon “cannot claim shock” that bathroom spycams were used as advertised
A West Virginia judge largely denied Amazon's motion to dismiss lawsuit.

Tech legal expert Eric Goldman wrote that a victory for the plaintiff could be considered "a dangerous ruling for the spy cam industry and for Amazon," because "the court’s analysis could indicate that all surreptitious hook cameras are categorically illegal to sell." That could prevent completely legal uses of cameras designed to look like clothes hooks, Goldman wrote, such as hypothetical in-home surveillance uses.
- Stop ChatControl!
Chat Control, the new EU law project to weaken messaging systems and get rid of E2E encryptions so as to scan in clients sides the content of the messages (but only for children safety, of course).
- France bans ministers from WhatsApp, Signal; demands French alternatives.www.politico.eu France bans ministers from WhatsApp, Signal; demands French alternatives
‘These digital tools are not devoid of security flaws,’ government document says.
After the Tchap project based on Matrix, the French Prime Minister asks anyone in the gouvernement to use Olvid, the only app validated by the ANSSI, with metadata encryption and no centralised architecture nor contacts discovery. But only the front-ends are open source, not the back-end.
Source: https://www.politico.eu/article/france-requires-ministers-to-swap-whatsapp-signal-for-french-alternatives/
- What are good YubiKey alternatives with NFC and biometrics?www.yubico.com USB-C YubiKey 5C NFC Two-Factor Security Key | Yubico
Protect yourself from account takeovers with the efficient, multi-protocol YubiKey 5C NFC. Go passwordless with our NFC capable security key today.

Hey everyone,
I am currently using an old(er) HYPERSECU FIDO key, USB-A with a button, and I am looking to
- secure my phone as well (NFC) and, if possible
- add biometric authentication to the mix.
Are there good alternatives or better: upgrades to the YubiKey which do support NFC as well as biometrics and come with a USB-C?
Thanks for your time 👋
- How safe is Webview browser
cross-posted from: https://programming.dev/post/6272443
> After trying different browsers on android I found Privacy Browser to be what I need. > It have encrypted backups,Domain settings,jsless by default,Deleting all site data and Most usable UI. > Only issue is It is based on webview and I am using system default webview as my device is nonrooted so how secure is to go this way?
- WTF website certificates chain of trust...
cross-posted from: https://programming.dev/post/6002270
> Hi, > > If you don't know how work the
chain of trustfor the httpS > > You might want to watch this video > https://invidious.privacydev.net/watch?v=qXLD2UHq2vk > ( if you know a better one I'm all ears ) > > So in my point of view this system have some huge concerns ! > > 1. You need to relies to a preinstalled store certificate in your system or browser... > Yeah but do you know those peoples ??!! it might seem weird, but actually you should TRUST people that YOU TRUST/KNOW !! > > Here an extract from the certificate store om Firefox on Windows. > > ! > > I do not know ( personally ) any of those COMMERCIAL company ! > > 2. Of course we could use Self-certificate but this is not protecting against Man-in-the-middle_attack . Instead of using a chain (so few 3th party involved , so increasing the attack surface ! ) why not using something simpler !? like for example > * a DNS record that hold the HASH of the public key of the certificate of the website ! > * a decentralized or federated system where the browser could check those hash ? > > > Really I don't understand why we are still using achain of trustthat is > 1. not trusted > 2. increase the surface of attack > 3. super complex compare to my proposals ? > > Cheers, > > > > > > ::: spoiler Why I don't use the term SSL > Because actually httpS now use TLS not anymore ssl > https://en.wikipedia.org/wiki/Transport_Layer_Security > ::: - eIDAS 2.0 Sets a Dangerous Precedent for Web Securitywww.eff.org eIDAS 2.0 Sets a Dangerous Precedent for Web Security
The Council of the European Union this week adopted new language for regulations governing internet systems that may put the security of your browser at greater risk.The new language affects the EU’s electronic identification, authentication and trust services (eIDAS) rules, which are supposed to...

With a new open letter of specialists and engineers against that hazardous project
https://nce.mpi-sp.org/index.php/s/cG88cptFdaDNyRr
- Flash LineageOS on old devicewrite.as LineageOS = ❤ (a step by step guide)
🇺🇸 - Thursday, October, 10th 2019 Keywords: #LineageOS, #Cyanogen, #Android, #ROM, #AOSP Protect your privacy, get rid of blobs with unknown-to-you behaviors, decrease t...

Just wanted to share kind of tutorial I wrote about flashing LineageOS on old smartphones to keen them up to date 📱
- Privacy or sensitive data… a list of tools to protect your дѕѕwrite.as Privacy or sensitive data… a list of tools to protect your дѕѕ
- Friday, August, 17th 2018 Keywords: #privacy, #data, #censorship, #surveillance, #freedom Sometimes friends of mine asked me why I am so interested in subjects and tools related to privacy, data a...

Just wanted to share an old but still relevant publication about tools to use to protect our privacy, feel free to comment and share suggestions 😁
- Using teletext to escape voice printing
cross-posted from: https://fedia.io/m/disabled/t/346115
> Banks have started capturing customers voice prints without consent. You call the bank and the robot’s greeting contains “your voice will be saved for verification purposes”. IIUC, these voice prints can be used artificially reconstruct your voice. So they could be exfiltrated by criminals who would then impersonate you. > > I could be wrong about impersonation potential.. just fragments of my memory from what I’ve read. In any case, I don’t like my biometrics being collected without my control. > > The countermeasure I have in mind is to call your bank using #Teletext (TTY). This is (was?) typically a special hardware appliance. As a linux user, TTY is what the text terminal is based on. So I have questions: > > 1. can a linux machine with a modem be used to convert a voice conversation to text? > > 2. how widespread are TTY services? Do most banks support that, or is it just a few giant banks? > > 3. if street-wise privacy enthusiasts would theoretically start using TTY in substantial numbers, would it help the deaf community by increasing demand for TTY service, thus increasing the number of businesses that support it?
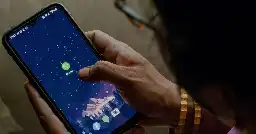
- Inside the deadly instant loan app scam that blackmails with nudeswww.bbc.com Inside the deadly instant loan app scam that blackmails with nudes
At least 60 people have killed themselves in India after being extorted by a global racket.

Cross post from r/privacy
- Backdoored firmware lets China state hackers control routers with “magic packets”arstechnica.com Backdoored firmware lets China state hackers control routers with “magic packets”
The modified firmware used by BlackTech is hard to detect.

- I Tested an HDMI Adapter That Demands Your Location, Browsing Data, Photos, and Spams You with Adswww.404media.co I Tested an HDMI Adapter That Demands Your Location, Browsing Data, Photos, and Spams You with Ads
The cord is detected as a "computer" and tracks “favorite videos, videos watched, and bookmarks,” as well as “Location Data, Sensor Data, Tracking Cookies Data, and Installed Apps Data.”

- Leaked screenshot shows Amazon is now tracking individual employee office attendance records, reversing its anonymized data policywww.businessinsider.com Leaked screenshot shows Amazon is now tracking individual employee office attendance records, reversing its anonymized data policy
Amazon is now sharing individual employee office attendance records in its latest move to force workers back to the office.

- Neither Inviduous nor piped is working
From some days I have seen that piped never works and invidious works for 1/10 times.Is it due to instances are down or google is doing something.
Or is it my internet issue 🥲 Is it working for others.
- Will using android without google account decrease number of privacy concerns

Title + As I dont have a G account signed in they cant track me as a person and I also turned diagnostics data sharing off. Will it be help they might track me a as person on this device.Right?? Also as to quit google I have to quit internet so will it be advantageous to do this thing.
- Google’s data trade, E2E encryption victory, rumors of ads in WhatsApp, and X’s risky verificationadguard.com New EU law, OpenAI vs. news media, WhatsApp, Twitter, and Texas
EU users are given a chance to kick the social media habit — will they seize it? OpenAI faces mounting backlash from news media over data scraping, and WhatsApp is about to make your calls a little more private.

TL;DR
> Google’s ‘ad auctions’ face a privacy challenge in the Netherlands. Google has been accused of intrusive online surveillance by more than 82,000 people who have signed up to a class action lawsuit against the tech giant in the Netherlands.
> Adobe starts paying out stock contributors for helping train AI. To train Firefly, its generative AI model, the company only uses content that it has rights to through its stock image platform Adobe Stock or that is in the public domain. Adobe has now started to make good on its promise to compensate Adobe Stock creators who may lose out from the widespread adoption of AI.
> UK backs down on encryption-breaking plan. The plan was to compel service providers, including messengers, to scan encrypted chats for child porn. Although the British government promised not to force companies to use unproven technology to snoop on users, it may try to enforce the so-called “spy clause” in the future if better and more secure (in the government’s eyes) technology emerges.
> WhatsApp denies it will have ads. The Financial Times has reported that WhatsApp is considering inserting ads into lists of conversations with contacts in a bid to increase its revenue. A rebuttal from WhatsApp head Will Cathcart followed. “This @FT story is false. We aren’t doing this.” Still, the FT stood by their story, claiming that before it was published they had reached out to WhatsApp, and they had not denied such conversations could have taken place. Citing sources within WhatsApp, the FT then reported that another option that was being discussed is to introduce a paid ad-free version of WhatsApp.
> X unveils verification system based on govt. ID. X, formerly Twitter, has begun offering its paid subscribers a new way of verification. Now, they can upload their government-issued IDs along with their selfie, and get an “ID verified” label on their profile along with “prioritized support.”
- Is google actually that evil?
Hi I recently reviewed my Google account settings on my phone. On exploring it I found that I can Remove almost every annoying tracker,I can delete my data,Remove services,Disable Personised ads etc.After giving it 20minutes of my day I found that Google do not deserve the Hate it gets from FOSS and PRIVACY Consious people.Is there some real reason why you should not use google products for privacy or It is just everybody want to live a Hacker's life.
- A long list of tech companies are rushing to give themselves the right to use people's data to train AIwww.businessinsider.com A long list of tech companies are rushing to give themselves the right to use people's data to train AI
More companies are quietly giving themselves permission to use consumer data to train generative AI models and tools.

- Carmakers are failing the privacy test. Owners have little to no control of the data they hand overwww.ctvnews.ca Carmakers are failing the privacy test. Owners have little to no control of the data they hand over
Cars are getting an 'F' in data privacy. Most major manufacturers admit they may be selling your personal information, a new study finds, with half also saying they would share it with the government or law enforcement without a court order.

- A little more on the Google DRMadguard.com Google wants to kill open Web under the guise of making it safer
A group of Google engineers has proposed a new Web API that threatens to uproot the work of apps and browsers if they interfere with its ad business. Will the open Web survive?

- Tiktok is at it againadguard.com TikTok tracked a cat’s account to spy on its owner. Is your privacy at risk?
A journalist was spied on by TikTok because she let her cat loose on the video-sharing platform. How did this happen? And what can you do to limit social media tracking and your chances of being spied on?

I know it's not exactly hot news, but I entirely missed the article, so here you go.
- Norway Took On Meta’s Surveillance Ads and Wonwww.wired.com Norway Took On Meta’s Surveillance Ads and Won
Meta has long fought Europe's demands that it get people's consent before using their data for targeted ads. Then a Norwegian regulator threatened fines of $100,000 per day.

- A New Decentralized Application Framework
From Cult of the Dead Cow, Veilid allows anyone to build a distributed, private app. Veilid will give users the privacy to opt out of data collection, and online tracking. Veilid is being built with user experience, privacy, and safety as our top priority. It will be open sourced and available to everyone to use and build upon, with flagship apps available from the launch.
- Hacking group plans system to encrypt social media and other appswww.washingtonpost.com Hacking group plans system to encrypt social media and other apps
The hacktivist group Cult of the Dead Cow will release details about the system at Def Con next week.



